ACPlus®
Security and HIPAA Compliance
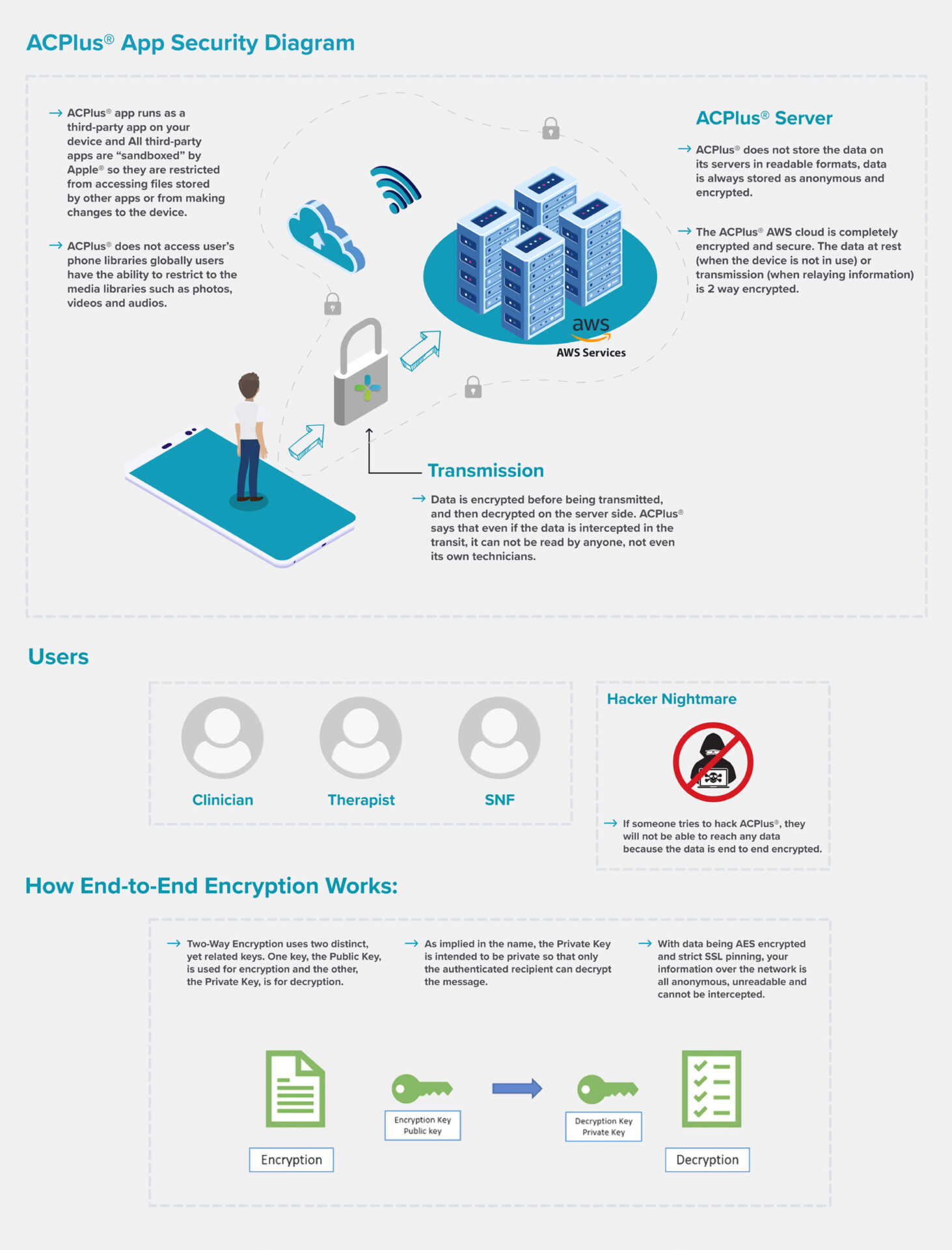
This page contains the ACPlus® application security overview. The goal of this page is to provide a high-level overview of encryption and security methods installed across the entire ACPlus® platform to ensure HIPAA compliancy.
DATA PRIVACY
- iOS and iPadOS® will not allow users to install potentially malicious unsigned apps or to run untrusted apps. ACPlus® is a trusted app and only available on the Apple® App Store®. This is centrally managed by Apple at the operating system level.
- ACPlus® connects directly to the cloud, bypassing users’ mobile device photo, video and audio libraries. Users’ are able to use their devices without further restrictions.
LOCATION TRACKING
- There is no location tracking. ACPlus® will never access the user’s location.
STORING PERSONAL INFORMATION AND CACHE MANAGEMENT
- There is no caching; no personal information is stored locally. All information is readable only at the time the screen is in foreground and when the app is running. All data is encrypted (the data is scrambled), so ‘over the shoulder’ viewing is the only way to intercept patient information.
USER ACCOUNTS AND PASSWORDS SECURITY
- The application is using the SRP (secure remote password) authentication mechanism of Amazon Web Service’s AWS Cognito, where a real password is never stored on the user’s phone or local database, so there is no case of keeping a password unprotected (plain text).
- After login, another layer of account security is installed which is multi-factor authentication and this is achieved by sending OTP (unique codes) to the user’s email addresses or phone number.
- In case of forgetting a password or needing to reset a password, the user’s identity is validated prior to resetting a password. As a control, AWS Cognito uses two-factor authentication (2FA) where a code is sent via email or phone number to confirm the user identity.
DATA TRANSMISSION AND PROTECTION
- All data transmissions are two-way AES encrypted using 256-bit encryption.
- The ACPlus® app runs as a third-party app on your device and all third-party apps are “sandboxed” by Apple® so they are restricted from accessing files stored by other apps or from making changes to the device. Sandboxing is designed to prevent apps from gathering or modifying information stored by other apps.
- Whether you are using a managed or public device, or if you are using a public network, no one can steal Information due to the end-to-end encryption (this prevents a malicious user from ‘sniffing’ your data). On a public network, your data information is safe. With data being AES encrypted and strict SSL pinning, any information sent over any network is all anonymous, unreadable, and cannot be intercepted.
- The ACPlus® cloud protection is completely encrypted and secure. Similar to WhatsApp (a popular messaging app), the data at rest (when the device is not in use or transmission (when relaying information) is two-way encrypted.
HIPAA COMPLIANT
- ACPlus® is HIPAA compliant ensuring the privacy and integrity of patient data (ePHI)
ACPlus® Frequently Asked Questions (HIPAA Privacy and Security)
1. What are the safeguards that allow therapists to access ACPlus® using their personal devices?
The ACPlus® app is designed so that no patient information is stored locally on any device that uses the app.
- Patient data is protected through transmission and at rest in accordance with the HIPAA Security Rule.
- Therapists will be trained in the appropriate use of the ACPlus® app.
- Review the Dos and Don’ts section for some best practices for use within HIPAA guidelines.
2. How is ePHI protected if I take a picture with the camera on my iPad or iPhone using the ACPlus® app?
Images taken on the ACPlus® application while using an iPad or iPhone are automatically sent securely to the encrypted ACPlus® cloud.
- Images are never stored locally on any device.
3. How is ACPlus® used for telehealth care or consultation and what precautions should users can take?
ACPlus® uses non-public facing, remote communication app Twilio for telehealth consultations. Twilio is HIPAA compliant.
- Healthcare providers should conduct telehealth in private settings, or office connecting to a patient who is at home or at another clinic/facility.
- If telehealth cannot be provided in a private setting:
- Implement reasonable HIPAA safeguards to limit incidental disclosures of protected health information (PHI).
- Safeguards include but are not limited to using non-public facing communication products, lowering voices, not using speakerphone or maintaining reasonable distance from others when discussing PHI.
4. How is ACPlus® assigned to a user and should that access be shared?
ACPlus® requires all users with authorized access (including employees) to have an individual login account.
- For set up, users are assigned individual access and can choose to use email, phone number, or a customized username along with password.
- Multi-factor authentication is required to access the ACPlus® environment.
- ACPlus® is not meant to be used by multiple users using the same log on ID or user ID.
- Administrators who assign access for users must assign each user their own log-in and user ID in accordance with ACPlus® contractual requirements.
- System access and activity can be identified and tracked by user.
5. How does the HIPAA rule allow health care providers to use mobile devices to access ePHI in a cloud?
Health care providers, other covered entities, and business associates may use mobile devices to access (ePHI) in a cloud as long as:
- Appropriate physical, administrative, and technical safeguards are in place to protect the confidentiality, integrity, and availability of the ePHI on the mobile device and in the cloud.
- Appropriate BAAs are in place with any third party service providers for the device and/or the cloud that will have access to the ePHI.
Data backup and storage
6.1 How and how often is ePHI backed up to prevent data loss?
ACPlus® uses the AWS RDS database for data storage.
- The routine backups are managed by AWS. The database is configured for daily automated backups.
- The copy of the backup file is stored by AWS.
6.2 Where is this backed up data stored and who has access to it?
Using the backup file, the database with ePHI can be restored or rolled back to the prior version within the 35-day backup retention period.
- Only authorized users (AWS administrators and authorized IAM users) can access the RDS resources.
Storage of ePHI
7.1 How is ePHI be stored?
The stored data is encrypted, de-identified and made unreadable, thus HIPAA compliant.
Audit controls
8.1 Who has access to the data other than individual users?
Nobody has access to the data other than individual users.
- All the system level logs are stored in the ACPlus® Cloud.
- ACPlus® uses AWS CloudWatch and CloudTrail services that monitor all inbound activities in the cloud including audit trails, management supervision, or system-level monitoring.
8.2 How are user logins monitored?
ACPlus® also maintains a secure custom event logging system that displays the user level logs at the Facility Portal.
- This log is stored anonymously in the ACPlus® database and includes the user ID, event ID, event performed, and date/time of the events. (The logs do not contain any patient’s personal information).
- AWS Cognito tracks user login sessions and all sessions are monitored/ tracked in the AWS Cloud.
- ACPlus® Administrator can review and summarize login sessions on the ACPlus® CMS (Customer Management System) upon request
ACPlus® User Dos & Don’ts
DO
- Log in to ACPlus® using your unique user account
- Logout of ACPlus® when not actively using the application
- Be sure to follow all HIPAA guidelines when using the ACPlus® application
- Assure that when reviewing or accessing patient information (ePHI), that only you can visually or audibly review the ePHI.
- Be aware of your surroundings for others looking over your shoulder when viewing ePHI
DON’T
- Share log in information or password with any other user
- Leave your device unattended at any time
- Screen shot copy, or share any ePHI from the ACPlus® application
- Email any ePHI from ACPlus® without consulting your company’s HIPAA guidelines first
- Use other third party, public facing applications (as discussed above) to transmit or communicate any ePHI.